Ok, so you’ve played Combat Mission for a while now and have figured out how to move your units around, give them fire orders, and make stuff go boom. But you find yourself at the beginning of every scenario wishing you had some handy advice or guidelines on how to actually plan a movement to contact or to seize the village just over the ridge, all the while keeping your casualties to a minimum. These tutorials are designed specifically for you, my friend! While avoiding game mechanics and doctrinal theory, I want to present “a way ahead” so to speak for players who may not be all that versed in military tactics.
The tricky thing to understand about tactics is that there is no “book answer.” Most everyone is familiar with sports so I will use that worn out analogy. A football, basketball, whateverball coach always has a playbook full of detailed plans on what he wants his players to do, all designed to give an edge over the opponent team. The opposing team is also following a playbook and is implementing a plan. But as any casual observer knows, once the ball is in motion those plans require constant modification by the players. This usually disrupts both side’s plans and the players (usually with some direction from the team leadership on the field) have to adapt to the changing situation quickly. But without the initial plan the team would have never been able to even begin to move forward effectively. It is impossible for a coach (or a doctrine writer) to anticipate all that can happen on the field and develop a plan for each scenario accordingly. So for any given situation there is no “book answer.” Instead what we have are guidelines, concepts and drills that help us develop a plan and then react effectively when the situation changes.
In layman’s terms tactics can really be divided into two categories. I will call these (1) Planning Considerations and (2) Battle Drills (I am in no way using these in a doctrinal manner hence the use of the term layman). Planning Considerations are the meat and potatoes that a commander (platoon, company, or battalion) uses to draw up his plan for an operation. He has a playbook that lays out a template for how to conduct a defense, a deliberate attack, urban operations, etc. It is then up to him to study the terrain, enemy situation, his forces, and his specific mission and using the template as a guide, develop a plan that will work and preserve his force. These tutorials will provide the CMSF player with those templates. The second category is Battle Drills. These come into play after the initial plan is started and really apply below the platoon level. Though a company sized organization can have a battle drill for, say, occupy assembly area or refueling operations, these are usually called Standard Operating Procedures (SOPs). SOPs are essentially Battle Drills on a bigger scale. Battle drills are so universal the US Army only has 8 or so. (Doctrine is very fluid these days due to a constantly changing operating environment.) Everyone in the Army receives training in these battle drills at some point but they are the granite base that every combat arms leader builds on. Drills are what a unit executes when faced with an enemy force that wasn’t planned for. The unit may be able to overwhelm the enemy force or simply fix them so that a higher HQ can make an assessment and modify or scrap the plan. Drills are usually trained to such a degree that every soldier knows what to do next. Basically when you order a tank in CM to crest a hill and the tank fires at an enemy vehicle that it spots, it is conducting a React to Contact Drill, all without you having to do anything. This takes some of the effect out of the surprise that comes with stumbling into an enemy unit that wasn’t expected. I will not spend a lot of time on Drills since they are usually what occur between your friendly lines and the objective. CM really covers the “last hundred yards” so to speak, or the actions on the objective. Most of what you will want to do in the 30-45 minutes of a CM scenario can be preplanned, so battle drills rarely come into play. I will focus on Planning Considerations for a variety of missions, but first we need to hit some theory and doctrine with a broad brush.
Theory/Doctrine
These are the all-encompassing terms and theories that frame any discussion of tactics and so therefore need to be addressed.
Principles of War: First penned by Clausewitz, most armies have a short list of principles that they use to build a framework for analyzing and discussing military operations. Here is the Wikipedia link that lists some of the most prominent (I, of course, am really only familiar with the US list).
Read these and become familiar with them, at the very least you will sound impressive next time the water cooler discussion turns to military news. Seriously though, if you want to really understand how an army thinks and fights these fundamentals are essential.
Tenets of Army Operations: Add these to the list. This is the list of the “must haves” for successful operations. Usually when a defeated party analyzes why they lost the reason will be one of these.
Offensive Operations
Chapter 4, FM 3-21.10 27 July 2006
CHARACTERISTICS
4-1. The characteristics of the offense are surprise, tempo, concentration, and audacity. Due to the nature of modern offensive operations, flexibility is included in the following discussion of the offense. For each mission, the commander decides how to apply these characteristics to focus the effects of his combat power against enemy weakness. Detailed planning is critical to achieve a synchronized and effective operation. Instead of ‘fighting the plan,’ commanders should exploit enemy weaknesses.
SURPRISE
4-2. Units achieve surprise by striking the enemy at a time, place, or manner in which he is unprepared. Total surprise is rarely essential or attainable. Simply delaying or disrupting the enemy's reaction by attacking where he least expects is usually effective. Surprise delays the enemy's reactions, stresses his command and control, and induces psychological shock in enemy soldiers and leaders. Surprise may allow an attacker to succeed with fewer forces. The company's ability to attack in limited visibility or through restrictive terrain, to operate in small units, and to infiltrate are often key to achieve surprise. The company must exploit the effects of surprise before the enemy can recover.
TEMPO
4-3. Tempo is the rate of military action relative to the enemy. Tempo is not the same as speed. Controlling or altering tempo is essential for maintaining the initiative. Tempo promotes surprise, keeps the enemy off balance, contributes to the security of the attacking force, and prevents the defender from taking effective countermeasures. By increasing tempo, commanders maintain momentum.
4-4. When properly controlled and exploited, tempo confuses and immobilizes the defender until the attack becomes unstoppable. Leaders build tempo into operations through careful planning, synchronization, coordination, and transition to the next operation.
4-5. The company increases its tempo by using simple plans, quick decision making, decentralized control, mission orders, and rehearsed operations. The company maintains tempo by ensuring sustainment operations are well coordinated and continuous, thus preventing culmination.
CONCENTRATION
4-6. The attacker masses the effects of combat power at the decisive point to achieve the unit's purpose. Leaders concentrate the effects of their combat power, while trying not to concentrate forces.
4-7. Because the attacker often moves across terrain the enemy has prepared, he might expose himself to enemy fires. By concentrating overwhelming combat power at a weak area or system, the attacker can reduce the effectiveness of the enemy fires and the amount of time he (the attacker) is exposed to enemy fires.
4-8. The challenge for the company commander is to concentrate combat power, while reducing the enemy's ability to do the same against the friendly unit. Actions that cause the enemy to shift combat potential away from the intended decisive point yield a greater advantage, for example, moving dispersed, but concentrating at the last moment and using deception. The commander employs his Infantry capabilities to achieve overwhelming combat power at the decisive point.
AUDACITY
4-9. Audacity is a simple plan of action, boldly executed. The audacious commander develops confidence by conducting a thorough estimate. His actions, although quick and decisive, are based on a reasoned approach to the tactical situation and on his knowledge of his Soldiers, the enemy, and the terrain. He is daring and original, but he is not rash.
4-10. Audacious commanders throughout history have used the indirect approach. They maneuver to maintain a position of advantage over the enemy, seek to attack the enemy on the flank or rear, and exploit success at once, even if this briefly exposes their own flanks.
4-11. Boldness and calculated risks have always been the keystones of successful offensive operations. However, risks must be consistent with the higher commander's mission and intent. Commanders dispel uncertainty through action; they compensate for a lack of information by seizing the initiative and pressing the fight.
FLEXIBILITY
4-12. Although not a characteristic of the offense, FM 3-90 (Tactics) says that flexibility bears discussion. At some point in most attacks, the original plan must be adjusted to meet changes in the situation. The commander maintains flexibility at all times so he can attack identified enemy weaknesses when they are presented. The commander should avoid ‘fighting the plan’ and instead focus on fighting the enemy or attacking identified enemy weaknesses. Mission orders, a clear commander's intent, and competent subordinate leaders who exercise initiative ensure that proper adjustments are made.
4-13. The commander and subordinate leaders must expect uncertainties and be ready to exploit opportunities. The flexibility required often depends on the amount of reliable intelligence the commander has on the enemy.
4-14. The commander builds flexibility into his plan during the MDMP. By conducting a thorough war game and rehearsals, he develops a full appreciation for possible enemy actions. A reserve increases the company commander's flexibility.
TYPES
4-15. The four types of offensive operations, described in FM 3-90, are movement to contact (MTC), attack, exploitation, and pursuit. Companies can execute MTC and attack.
ATTACK
4-16. An attack is an offensive operation that destroys enemy forces, seizes or secures terrain, or both. Movement, supported by fires, characterizes the conduct of an attack. The company will likely participate in a synchronized attack. However, a company may conduct a special purpose attack as part of, or separate from, an offensive or defensive operation. Special purpose attacks consist of ambush, spoiling attack, counterattack, raid, feint, and demonstration.
MOVEMENT TO CONTACT
4-17. An MTC is a type of offensive operation designed to develop the situation and establish or regain contact. The company may conduct an MTC on its own or as part of a larger unit's operation when the enemy situation is vague or not specific enough to conduct an attack.
FORMS OF MANEUVER
4-20. Each form of maneuver attacks the enemy differently. Each poses different challenges for attackers and different dangers for defenders. Maneuver places the enemy at a disadvantage through the application of friendly fires and movement. The five forms of maneuver follow.
ENVELOPMENT
4-21. Envelopment is a form of maneuver in which an attacking force seeks to avoid the principal enemy's defenses by seizing objectives to the enemy rear or flank in order to destroy him in his current positions (Figure 4-1). A successful envelopment requires discovery or creation of an assailable flank. The envelopment is the preferred form of maneuver because the enemy must fight in at least two directions and the attacking force tends to suffer fewer casualties while having the most opportunities to destroy the enemy. Envelopments focus on--
Seizing terrain.
Destroying specific enemy forces.
Interdicting enemy withdrawal routes.
4-22. Turning movement is a form of maneuver in which the attacking force avoids the enemy's principal defensive positions by seizing objectives to the enemy's rear and causing the enemy to move out of his current positions, or to divert major forces to meet the threat (Figure 4-2). For a successful turning movement, the unit trying to turn the enemy must attack something that the enemy will fight to save. This might be a supply route, artillery emplacement, or headquarters. In addition to attacking a target the enemy will fight to save, the attacking unit should be strong enough to pose a real threat to the enemy. The attacker seeks to secure key terrain deep in the enemy's rear and along his lines of communication. Faced with a major threat to his rear, the enemy is turned out of his defensive positions and forced to attack rearward.
INFILTRATION
4-23. Infiltration is a form of maneuver. In an infiltration, an attacking force moves undetected into or through the enemy's main defenses, that is, an area occupied by an enemy forces. The purpose of an infiltration is to occupy a position of advantage in the enemy rear area to concentrate combat power against enemy weak points. Ideally, an infiltration exposes only small elements to enemy defensive fires (Figure 4-3). Moving and assembling forces covertly through enemy positions takes a lot of time.
A successful infiltration reaches the enemy's rear without fighting through prepared positions. A company may conduct an infiltration as part of a larger unit's attack with the battalion employing another form of maneuver. The company commander may also employ maneuver by infiltration to move his platoons to locations to support the battalion's attack. Companies can infiltrate--
To attack enemy-held positions from an unexpected direction.
To occupy a support-by-fire position to support an attack.
To secure key terrain.
To conduct ambushes and raids.
To conduct a covert breach of an obstacle.
PENETRATION
4-24. Penetration is a form of maneuver in which an attacking force seeks to rupture enemy defenses on a narrow front to create both assailable flanks and access to the enemy's rear (Figure 4-4). Penetration is used when enemy flanks are not assailable, when enemy defenses are overextended, when weak spots in the enemy defense are identified, and when time does not permit some other form of maneuver. A penetration normally consists of three steps.
1. Breach the enemy's main defense positions.
2. Widen the gap created to secure flanks by enveloping one or both of the newly exposed flanks.
3. Seize the objective. As part of a larger force penetration, the company will normally isolate, suppress, fix, or destroy enemy forces; breach tactical or protective obstacles in the enemy's main defense (secure the shoulders of the penetration); or seize key terrain. A battalion may also use penetration to secure a foothold within a large built-up area.
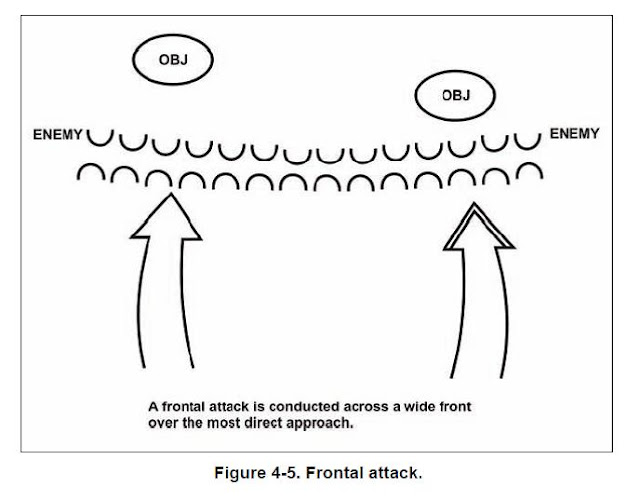
FRONTAL ATTACK
4-25. Frontal attack is a form of maneuver in which an attacking force seeks to destroy a weaker enemy force or fix a larger enemy force along a broad front. It is the least desirable form of maneuver, because it exposes the attacker to the concentrated fire of the defender and limits the effectiveness of the attacker's own fires. However, the frontal attack is often the best form of maneuver for an attack in which speed and simplicity are key; it helps overwhelm weak defenses, security outposts, or disorganized enemy forces.
Most CMSF offensive forms of maneuver will be Frontal Attack, Turning Movement and Envelopment. Mostly Frontal Attack due to the small map sizes in most of the scenarios. A penetration is really a higher level form of maneuver and Infiltrations would take forever and require a huge map.
Defensive Operations
The immediate purpose of defensive actions is to resist, defeat, or destroy an enemy attack and gain the initiative for the offense. Defensive operations defeat an enemy attack, buy time, economize forces, or develop conditions favorable for offensive operations. Defensive actions alone are not normally decisive; frequently, they are combined with or followed by offensive action. Though the outcome of decisive combat derives from offensive actions, commanders often find that it is necessary, even advisable, to defend. Once commanders make this choice, they must set the conditions for the defense in a way that allows friendly forces to withstand and hold the enemy while they prepare to seize the initiative and return to the offense. A thorough understanding of the commander's intent is especially critical in defensive operations, which demand precise integration of combat, combat service, and sustainment elements.
TYPES
5-1. As part of defensive operations, the company may defend, delay, withdraw, or counterattack. The company may also perform security tasks. The company normally defends, as part of the battalion's defense, in the main battle area (MBA). The three types of defensive operations are—
AREA DEFENSE
5-2. Concentrates on denying the enemy access to designated terrain for a specified time, rather than the outright destruction of the enemy.
MOBILE DEFENSE
5-3. Orients on the destruction of the enemy through a decisive attack(s) by a striking force.
RETROGRADE OPERATIONS
5-4. Forced or voluntary organized movements to the rear or away from the enemy.
PURPOSE
5-5. The immediate purpose of a defensive operation is to defeat an enemy attack and gain the initiative for offensive operations. The Infantry company may also conduct the defense to achieve one or more of the following purposes.
Gain time.
Retain key terrain.
Support other operations.
Preoccupy the enemy in one area while friendly forces attack him in another.
Erode enemy forces at a rapid rate while reinforcing friendly operations.
CHARACTERISTICS
5-6. The characteristics of the defense are also planning fundamentals for the Infantry company. These characteristics include preparation, security, disruption, massing effects, and flexibility. (FM 3-90 explains the two defensive patterns, area and mobile.)
PREPARATION
5-7. The defender arrives in the battle area before the attacker. He must take advantage of this by making the most thorough preparations for combat possible in the time available. By analyzing the factors of METT-TC, the Infantry rifle company commander gains an understanding of the tactical situation and identifies potential friendly and enemy weaknesses. He then war-games friendly and enemy options and synchronizes his concept of the operation with all available combat multipliers.
SECURITY
5-8. The goals of the company security effort are to deceive the enemy as to the location of friendly locations, strengths, and weaknesses. They also inhibit or defeat enemy reconnaissance operations. Security also provides early warning and disrupts enemy attacks early and continuously.
DISRUPTION
5-9. Defensive plans vary with the circumstances, but all defensive concepts of operation aim at disrupting the attacker's synchronization. Counterattacks, indirect fires, obstacles, and retention of key, or decisive terrain prevent the enemy from concentrating his strength against portions of the defense. Destroying enemy command and control vehicles disrupts enemy synchronization and flexibility.
MASSED EFFECTS
5-10. The successful defender concentrates combat power at the decisive time and place. Through massing effects, he can obtain a local advantage at points of decision. Offensive action and the use of surprise and deception are often the means of gaining this advantage. Concentration refers to combat power and its effects ― not just numbers of Soldiers and weapons systems. To concentrate combat power, the defender may economize in some areas, retain a reserve, and maneuver to gain local superiority. Local counterattacks might be needed to maintain the integrity of the defense. Indirect fire can shift to critical points to concentrate destructive effects rapidly.
FLEXIBILITY
5-11. Flexibility is derived from sound preparation and effective C2. The defender must be agile enough to counter or avoid the attacker's blow and then strike back effectively. Flexibility results from a detailed mission analysis, an understanding of the unit's purpose, aggressive reconnaissance and security, and when applicable, organization in depth and retention or reconstitution of a reserve. Flexibility requires that the company commander "see the battlefield"―physically and through timely and accurate reports. Supplementary positions on secondary avenue of approach may provide additional flexibility to the company commander. After proper analysis of the terrain and enemy situation, the commander can anticipate enemy actions and be prepared to act through the positioning of maneuver units or a reserve.
I included the paragraphs on type and purpose because when you are developing your defensive plan these will help you determine your overall scheme of the defense and assign purposes to your subordinate units.
The Basics
FM 3-21.71 MECHANIZED INFANTRY PLATOON AND SQUAD (BRADLEY)
Mounted Formations. When mounted, the platoon uses the column, wedge, line, echelon, coil, and herringbone formations (based on METT-TC factors).
(1) Column Formation. The platoon uses the column when moving fast, when moving through restricted terrain on a specific route, or when it does not expect enemy contact. Each vehicle normally follows directly behind the vehicle in front of it. However, if the situation dictates, vehicles can disperse laterally to enhance security. This is sometimes referred to as a staggered column. Figure 3-1 shows this type of column movement. The column formation has the following characteristics, advantages, and limitations:
• Control—Easy.
• Fires:
• Front and rear—Limited.
• Flank—Excellent.
• Security—Limited, overall.
(2) Wedge Formation. When the enemy situation seems unclear or when contact might occur, leaders often use the wedge formation shown in Figure 3-2. Both the platoon leader and platoon sergeant stay in the center of the formation, with their wingmen located to the rear of and outside of them. The wedge has the following characteristics, advantages, and limitations:
• Control—Easy.
• Fires:
• Front—Excellent.
• Flanks—Good.
• Security—Good, to flanks.
Figure 3-2
(3) Line Formation. When assaulting a weakly defended objective, crossing open areas, or occupying a support-by-fire position, the platoon mainly uses the line formation (Figure 3-3). The platoon can use the line formation in the assault to maximize the platoon’s firepower and shock effect. The platoon normally uses the line formation when no terrain remains between it and the enemy, when the platoon has suppressed the enemy’s antitank weapons, or when the platoon is vulnerable to artillery fire and must move fast. The line formation has the following characteristics, advantages, and limitations:
• Control—Difficult.
• Fires:
• Front and rear—Excellent (maximum firepower).
• Flank—Poor.
• Security—Less than other formations due to lack of depth.
Figure 3-3
(4) Echelon Formation. When the company team wants to maintain security or observation of one flank, and when the platoon does not expect enemy contact, the platoon uses the echelon formation (Figure 3-4). The echelon formation covers the exposed flank of a larger force well, and has the following characteristics, advantages, and limitations:
• Control—Difficult.
• Fires:
• Front—Excellent.
• Flanks—Excellent for echelon sides.
• Security—Good, for echelon sides of higher formation.
Figure 3-4
The Coil and Herringbone are formations at a halt and will not be used in CMSF.
3-3. MOVEMENT TECHNIQUES
The term “movement techniques” does not refer to the movement of fixed formations—it refers to the fluctuating distances between soldiers, teams, and squads. These distances vary based on the factors of METT-TC. As the probability of enemy contact increases, the platoon leader adjusts the movement technique to provide greater security. For example, if an enemy update received from higher headquarters states that the enemy has moved much closer to the platoon than the platoon leader anticipated, he immediately switches the platoon from traveling overwatch to bounding overwatch.
a. Traveling (Mounted). The platoon uses Traveling when contact with the enemy is not likely and speed is desired. The leader analyzes the latest information on the enemy and determines if contact with the enemy is unlikely.
b. Traveling Overwatch (Mounted). The platoon leader uses traveling overwatch when he thinks contact could occur. He designates one of his subordinate elements to provide security forward of the main body. In some cases, the improved awareness might prompt the security element to increase these distances. Leaders track the movement of forward security elements. They get position updates to ensure the forward security element remains on azimuth and within range of supporting direct fires.
c. Bounding Overwatch (Mounted). When the platoon leader expects enemy contact, he uses bounding overwatch. He initiates it based on planning information received earlier about the enemy situation and on SITREPs received during movement. He bounds elements using successive or alternate bounds.
(1) Before bounding, the leader shows the bounding element the location of the next overwatch position. Ideally, the overwatch element keeps the bounding element in sight.
(2) Once the bounding element reaches its overwatch position, it signals “READY” by voice or visual means to the element that overwatched it’s bound. The platoon leader makes sure the bounding element stays within two-thirds of the weapons range of the overwatch element.
Be sure to watch the attached video labeled “Movement Techniques.” It demonstrates all of the above with a Bradley Platoon. You see the plt moving down a road using traveling. As they near a potential danger area (a small town) the plt switches to Traveling Overwatch. The lead vehicle is pushed out ahead of the rest of the platoon as a sort of vanguard. The platoon stops short of the town and forms a line. The decision is made to bypass the town to the right using bounding overwatch. The platoon divides into two sections. One watches the danger area while the other bounds to the right and takes up a position covering the town. The other section then bounds past them. The platoon would continue this movement technique until contact with the enemy is made or the PL feels it is ok to downgrade to T.O.








No comments:
Post a Comment